Blogs
Stay Digitally Safe
 Quick Heal
Mar 31, 2026
Quick Heal
Mar 31, 2026
Homoglyph Attacks: How Lookalike Characters Are Exploited for Cyber Deception
Stay Digitally Safe
 Quick Heal
Feb 27, 2026
Quick Heal
Feb 27, 2026
Common Digital Payment Frauds in India and How to Stay Safe
Stay Digitally Safe
 Quick Heal
Feb 24, 2026
Quick Heal
Feb 24, 2026
Digital Bharat Needs Digital Trust: How Indians Can Protect Themselves Online
Stay Digitally Safe
 Quick Heal
Feb 04, 2026
Quick Heal
Feb 04, 2026
What Is a Supply Chain Attack? How It Works, Types, and How to Prevent It?
Stay Digitally Safe
 Quick Heal
Feb 02, 2026
Quick Heal
Feb 02, 2026
Passwordless Authentication: Meaning, Benefits & How It Works
Stay Digitally Safe
 Quick Heal
Jan 30, 2026
Quick Heal
Jan 30, 2026
How to Avoid Imposter Scams: Identify, Prevent & Stay Safe Online
Stay Digitally Safe
 Quick Heal
Jan 28, 2026
Quick Heal
Jan 28, 2026
Encrypted Phones Explained: How They Work & Why They Matter
Stay Digitally Safe
 Quick Heal
Jan 23, 2026
Quick Heal
Jan 23, 2026
Quick Heal: Digital Bharat ka Bharosa, Fraud se Suraksha
Stay Digitally Safe
 Quick Heal
Jan 22, 2026
Quick Heal
Jan 22, 2026
What Is Digital Security: Overview, Types, and Applications
Stay Digitally Safe
 Quick Heal
Jan 21, 2026
Quick Heal
Jan 21, 2026
Cyber Bullying: What It Is, How It Happens, and How To Stop It
AntiFraud
Stay Digitally Safe
 Aayush Chandhere
Aug 28, 2025
Aayush Chandhere
Aug 28, 2025
Lured by Luck: The Hidden Dangers of Lottery Scam
Stay Digitally Safe
 Quick Heal
Aug 14, 2025
Quick Heal
Aug 14, 2025
Types of Malware in Cybersecurity: Spyware, Adware and Ransomware
Stay Digitally Safe
 Quick Heal
Aug 14, 2025
Quick Heal
Aug 14, 2025
Endpoint Protection: Safeguard Laptops, Desktops, and Mobiles in Your Office
AntiFraud
 Subhrojyoti Chowdhury
Aug 13, 2025
Subhrojyoti Chowdhury
Aug 13, 2025
Unmasking Imposter Scams: A Dive into Social Engineering and Spoofing Tactics
AntiFraud
 Ayush Sonavane
Aug 07, 2025
Ayush Sonavane
Aug 07, 2025
Guarding Our Elders: A Comprehensive Report on the Elder Fraud Epidemic in India
AntiFraud
 Subhrojyoti Chowdhury
Aug 06, 2025
Subhrojyoti Chowdhury
Aug 06, 2025
Deciphering the KYC Scam Paradigm: An In-Depth Exploration of Threat Vectors and Mitigation Strategies
Stay Digitally Safe
 Quick Heal
Aug 06, 2025
Quick Heal
Aug 06, 2025
AI Powered Threat Detection: Stopping Deepfakes and Malware Before They Strike
Stay Digitally Safe
 Quick Heal
Aug 05, 2025
Quick Heal
Aug 05, 2025
Internet Security Vs Total Security? Let’s Find the Right Plan for You
Stay Digitally Safe
 Quick Heal
Aug 05, 2025
Quick Heal
Aug 05, 2025
Threat Detection and Response: What It Means and Why It Matters
Stay Digitally Safe
 Quick Heal
Aug 05, 2025
Quick Heal
Aug 05, 2025
Cryptography in Cybersecurity: Its Role in Antivirus Protection
Cyber Frauds
 Quick Heal
Aug 05, 2025
Quick Heal
Aug 05, 2025
AI Chatbot Scams Exposed: How Fake Bots and Assistants Are Tricking Millions
AntiFraud
 Quick Heal
Aug 01, 2025
Quick Heal
Aug 01, 2025
Synthetic Identity Fraud: Role of Anti-Fraud Tools in Unmasking Cybercriminals
AntiFraud
 Ayush Sonavane
Jul 31, 2025
Ayush Sonavane
Jul 31, 2025
Tech Support Scams: A Comprehensive Guide to Cybersecurity Awareness
AntiFraud
Stay Digitally Safe
 Subhrojyoti Chowdhury
Jul 24, 2025
Subhrojyoti Chowdhury
Jul 24, 2025
Crypto Mirage: Unmasking the Billion-Dollar Illusion of Investment Scams
Cyber Frauds
 qhblogadmin
Jul 21, 2025
qhblogadmin
Jul 21, 2025
Android Cryptojacker Disguised as Banking App Exploits Device Lock State
AntiFraud
 Ayush Sonavane
Jul 16, 2025
Ayush Sonavane
Jul 16, 2025
The Merge Call Scam Deconstructed: How Social Engineering Hijacks OTPs
Stay Digitally Safe
 Quick Heal
Jun 26, 2025
Quick Heal
Jun 26, 2025
Phishing Detection: Spot Hidden Dangers of ‘Urgent’ Messages Scams
AntiFraud
 Quick Heal
Jun 26, 2025
Quick Heal
Jun 26, 2025
How Does Antivirus Software Work To Detect and Stop Malware in Real Time
AntiFraud
Cyber Frauds
 Quick Heal
Jun 17, 2025
Quick Heal
Jun 17, 2025
The Holy Money Heist – Kedarnath Helicopter Ticket Booking Scams Uncovered!
AntiFraud
Cyber Frauds
What's in News
 Quick Heal
Jun 06, 2025
Quick Heal
Jun 06, 2025
Digital Arrest – Protect Yourself from Sophisticated Cyber Fraud
Stay Digitally Safe
 Quick Heal
May 28, 2025
Quick Heal
May 28, 2025
Protect Personal Data with Device Locks and Screen Protectors
Cyber Frauds
 Quick Heal
May 27, 2025
Quick Heal
May 27, 2025
How to Detect and Report Cyberstalking: Essential Cybersecurity Measures
Cyber Frauds
 Quick Heal
May 27, 2025
Quick Heal
May 27, 2025
Pirated Software Risks: Why Using It Puts Your Cybersecurity at Risk
Tips
 Quick Heal
May 27, 2025
Quick Heal
May 27, 2025
Why You Should Never Click on Suspicious Links in Text Messages: A Complete Guide
Cyber Frauds
 Quick Heal
May 27, 2025
Quick Heal
May 27, 2025
How Poor Cyber Hygiene Can Leave You Vulnerable to Cyberattacks
Cyber Frauds
 Quick Heal
May 27, 2025
Quick Heal
May 27, 2025
The Role of GDPR in Strengthening Data Protection & Cybersecurity Today
Tips
 Quick Heal
May 27, 2025
Quick Heal
May 27, 2025
Exploring the Different Types of Firewalls and Their Benefits in Cybersecurity
Stay Digitally Safe
 Quick Heal
May 27, 2025
Quick Heal
May 27, 2025
Why Quick Heal Stands Out as the Number One Antivirus Solution
Cyber Frauds
 Quick Heal
Apr 29, 2025
Quick Heal
Apr 29, 2025
The Rise of Mobile Banking Malware: Keeping Your Finances Secure
Cyber Frauds
 Quick Heal
Apr 28, 2025
Quick Heal
Apr 28, 2025
Recent Parcel Fraud Trends: Insights from Quick Heal’s Advisory
Stay Digitally Safe
 Quick Heal
Apr 28, 2025
Quick Heal
Apr 28, 2025
How to Check for Malicious Email Attachments? Tips for Staying Safe
Stay Digitally Safe
 Quick Heal
Apr 28, 2025
Quick Heal
Apr 28, 2025
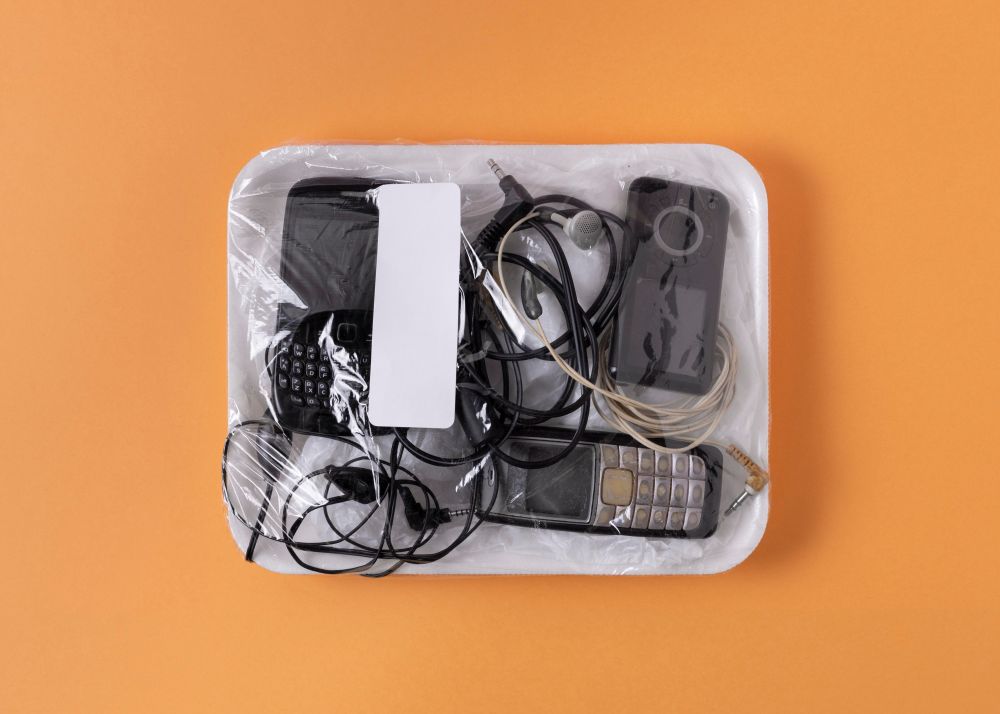
How to Safely Dispose of Old Devices: Protecting Your Data During Transition
Cyber Frauds
 Quick Heal
Apr 25, 2025
Quick Heal
Apr 25, 2025
Trading Scams: List of Fake Trading Websites and Tips for Safe Online Trading
Cyber Frauds
 Quick Heal
Apr 25, 2025
Quick Heal
Apr 25, 2025